by
United States Marine Field McConnell
Plum City Online - (AbelDanger.net)
July 7, 2016
1. Abel Danger (AD) claims that Hillary Clinton asked her State Department agent – Base One Technologies – to scrub the private servers on which she had carelessly allowed donors to the Clinton Foundation to develop false-flag attacks on her fellow Americans.
2. AD claims that Serco has been mentoring Base One Technologies – a woman-owned 8(a) company launched by the Clinton State Department on February 15, 1994 – as it tried to link thousands of wrongful deaths with crisis actors at mass-casualty events.
3. AD claims that Serco provided Zulu timing signals through Hillary Clinton's servers to Base One so it could stage, synchronize and execute false-flag attacks attributed to ISIS and spot fix times of deaths of victims for real-time wagering at the Clinton Foundation.
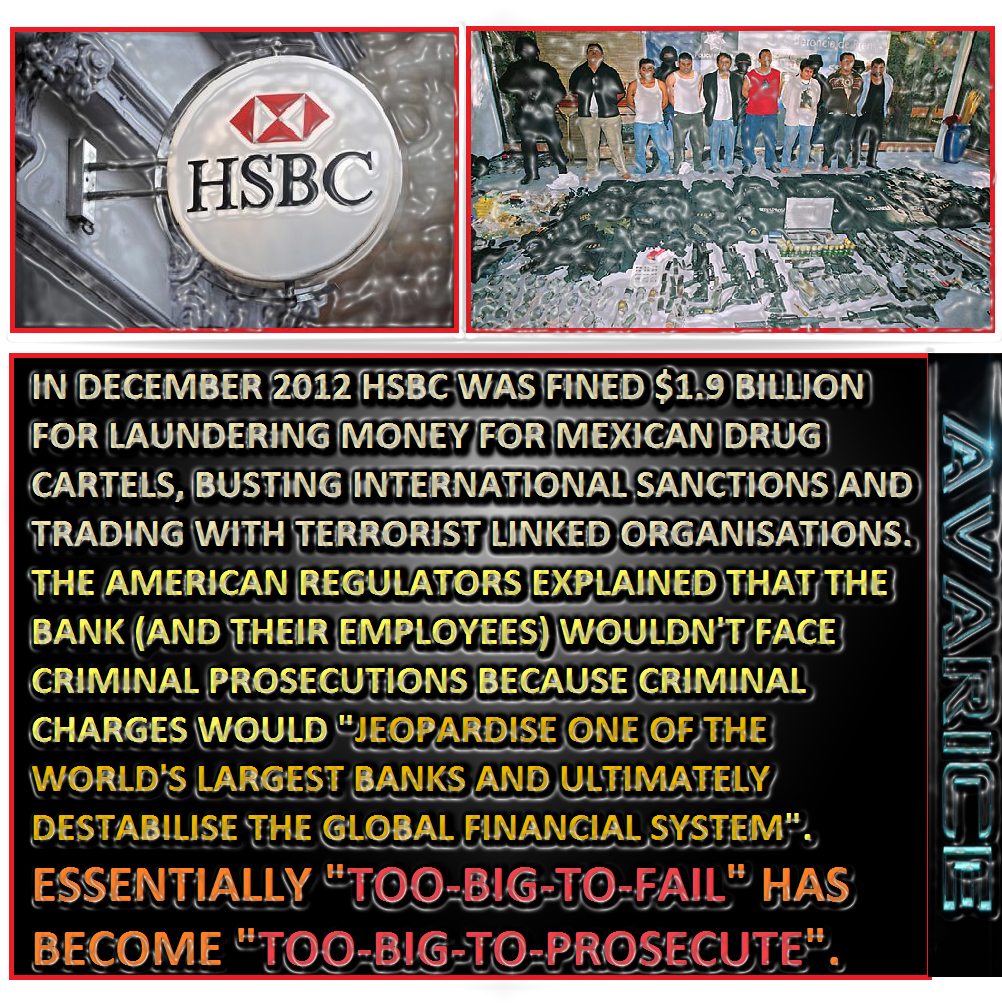
4. United States Marine Field McConnell asks James Comey – a former director of Serco's banker HSBC and the current FBI director – to hand over evidence of Clinton's extreme carelessness in the use of the servers to the families of those killed in ISIS attacks so they can develop class-action suits for the wrongful death of their relatives. (http://www.abeldanger.net/2010/01/field-mcconnell-bio.html).
(HACKED VIDEO) FAKED IN CIA STUDIO (JIHADI JOHN)!
[Check] Sophye e homenagem a Maureen Baginski
FBI Director Comey Recommends No Criminal Charges Over Clinton Emails
Copy of SERCO GROUP PLC: List of Subsidiaries AND Shareholders!
(Mobile Playback Version)
White's Club death-bet bookmaker services dates back to 1743 and – as Cameron's friend, Churchill's grandson and Serco CEO Rupert Soames well knows – only the technology to spot fix the Zulu time of victim death has changed.
Serco... Would you like to know more?
Defense Ammunition Center [Outsourced to Serco]
"Base One Technologies, Ltd. is a DOMESTIC BUSINESS CORPORATION, located in New York, NY and was formed on Feb 15, 1994. This file was obtained from the Secretary of State and has a file number of 1795583.
This business was created 7,695 days ago in the New York SOS Office and the registered agent is C T Corporation System that does business at 111 Eighth Avenue , New York in New York.
After conducting a search for principals and owners of Base One Technologies, Ltd., we were able to find 2 owners and/or executives. Their information is listed below. This file was last updated on May 14, 2013.
Principals
Liza R Zaneri
Chief Executive Officer
15 Irving Place
New Rochelle, NY 10801"
"Serco's Office of Partner Relations (OPR) helps facilitate our aggressive small business utilization and growth strategies. Through the OPR, Serco mentors four local small businesses under formal Mentor Protégé Agreements: Three sponsored by DHS (Base One Technologies, TSymmetry, Inc., and HeiTech Services, Inc.,) and the fourth sponsored by GSA (DKW Communications, Inc.). Serco and HeiTech Services were awarded the 2007 DHS Mentor Protégé Team Award for exceeding our mentoring goals." http://www.dtic.mil/whs/directives/corres/pdf/100515p.pdf
"Hillary Clinton's Extreme Carelessness Sure Seems Like a Federal Felony
Why did the FBI recommend against prosecuting her for gross negligence in handling classified material?
Jacob Sullum|Jul. 6, 2016 6:30 am
Explaining why he decided not to recommend criminal charges against Hillary Clinton in connection with her use of an unsecured private email server as secretary of state, FBI Director James Comey contrasts her "extremely careless" handling of "very sensitive, highly classified information" with the "clearly intentional and willful mishandling of classified information" that has prompted federal prosecution in other cases. But that distinction does not really explain why Comey decided "no reasonable prosecutor" would bring a case against Clinton, since one of the statutes guiding the FBI's investigation, 18 USC 793, makes it a felony to "mishandle classified information either intentionally or in a grossly negligent way" (emphasis added), as Comey himself notes at the beginning of yesterday's statement. Maybe Comey perceives a difference between extreme carelessness and gross negligence, but if so he never bothered to elucidate it."
"FBI: No Indictment for Saggy Wife!
Andrew Anglin Daily Stormer
July 5, 2016
Sigh.
I knew it would go down like this.
But after the Phoenix meeting, I did have hope.
But it doesn't matter.
We're going to win outright.
RT:
Though FBI found that Hillary Clinton and her staff were "extremely careless" with State Department emails hosted on a private server, no criminal charges will be brought against the former secretary and current presidential candidate.
FBI found "several thousand" work-related emails that were not turned over to the State Department by Hillary Clinton, Comey said.
"Three of those were classified at the time," he added.
None of those emails were intentionally deleted to hide information, the FBI director said.
Though Clinton's lawyers scrubbed the email servers in a way that precluded further forensic examination, the FBI is confident "there was no intentional misconduct" by them, Comey said."
"ISIS & Jihadi John Beheading Videos Staged by Actors?
British newspaper The Daily Star has posted an article covering a viral video revealing the ISIS and Jihadi John videos are fake.
ISIS and Jihadi John Videos are Fake
The clip appears to show a TV set and film crew watching on as a Jihadi John-like figure stands next to a prisoner kneeling next to him.
The Islamic State (ISIS) beheading videos reviled millions around the world as they watched Jihadi John callously murder innocent civilians in the most barbaric way in the desert.
But this latest video suggests the videos may have been carried out by ACTORS.
Infowars
The newspaper omits the fact the video was retrieved from the French language edition of Sputnik News, an international multimedia news service launched by Rossiya Segodnya, an agency owned by the Russian government.
Sputnik News claims the video was hacked by the CyberBerkut group from the device of a Sen. John McCain staffer while on a trip to Ukraine. The pro-Russian hacktivist group primarily targets NATO websites and US military-industrial complex corporations, including Greystone Limited and Triple Canopy. It has also attacked the Ukrainian government and the German Chancellery and the German Bundestag."
"Islamic State of Iraq and the Levant
From Wikipedia, the free encyclopedia "ISIL", "ISIS", "Daish", "Daesh", and "Islamic state group" redirect here. For other uses, see ISIL (disambiguation), ISIS™ (disambiguation), Daish (disambiguation), and Islamic state (disambiguation).
Not to be confused with Islamic republic. The Islamic State of Iraq and the Levant (ISIL, IPA /ˈaɪsᵻl/), also known as the Islamic State of Iraq and Syria[note 1] (ISIS, /ˈaɪsᵻs/),[32] and by its Arabic language acronym Daesh (داعش dāʿish, IPA: [ˈdaːʕiʃ]),[33][34] is a Salafi jihadist militant group that follows a fundamentalist, Wahhabi doctrine.[35]
The group first began referring to itself as the Islamic State (الدولة الإسلامية ad-Dawlah al-Islāmiyah) or IS[36] in June 2014, when it proclaimed itself a worldwide caliphate,[37][38] and named Abu Bakr al-Baghdadi as its caliph.[39] As a caliphate, it claims religious, political and military authority over all Muslims worldwide.[40] The group's adoption of the name "Islamic State" and its idea of a caliphate have been widely criticised, with the United Nations, various governments, and mainstream Muslim groups rejecting its statehood or caliphhood.[41] As of December 2015, the group has control over vast landlocked territory in Iraq and Syria, with a population estimate ranging between 2.8 million[42] and 8 million people[43] where it enforces its interpretation of sharia law. ISIL affiliates control small areas of Libya, Nigeria and Afghanistan and operate in other parts of the world, includingNorth Africa and South Asia.[44][45][46]
ISIL gained prominence in early 2014 when it drove Iraqi government forces out of key cities in its Western Iraq offensive,[47] followed by the capture of Mosul[48] and the Sinjar massacre.[49] The subsequent possibility of a collapse of the Iraqi state prompted a renewal of US military action in the country. In Syria, the group has conducted ground attacks on both government forces and rebel factions. The number of fighters the group commands in Iraq and Syria was estimated by the CIA at 31,000, with foreign fighters accounting for around two thirds,[50] while ISIL leaders claim they command 40,000 fighters, with the majority of them being Iraqi and Syrian nationals.[27]
The group has been designated a terrorist organisation by the United Nations, the European Union and its member states, the United States, Russia,India, Indonesia, Israel, Turkey, Saudi Arabia, Syria, Iran and other countries. Over 60 countries are directly or indirectly waging war against ISIL. Adept at social media, ISIL is widely known for its videos of beheadings[51] of both soldiers and civilians, including journalists and aid workers, and its destruction of cultural heritage sites.[52] The United Nations holds ISIL responsible for human rights abuses and war crimes, and Amnesty International has charged the group with ethnic cleansing on a "historic scale" in northern Iraq.[53] Around the world, Islamic religious leaders have overwhelmingly condemned ISIL's ideology and actions, arguing that the group has strayed from the path of true Islam and that its actions do not reflect the religion's real teachings or virtues.[54]
The group originated as Jama'at al-Tawhid wal-Jihad in 1999, which pledged allegiance to al-Qaeda and participated in the Iraqi insurgency following the March 2003 invasion of Iraq by Western forces. Joining other Sunni insurgent groups to form the Mujahideen Shura Council, this group proclaimed the formation of the Islamic State of Iraq (ISI) in October 2006. In August 2011, following the outbreak of the Syrian Civil War, ISI, under the leadership of al-Baghdadi, delegated a mission into Syria, which under the name Jabhat an-Nuṣrah li-Ahli ash-Shām (or al-Nusra Front) established a large presence in Sunni-majority Al-Raqqah, Idlib, Deir ez-Zor, and Aleppo provinces. The merger of ISI with al-Nusra Front to form the "Islamic State of Iraq and the Levant" (ISIL), as announced in April 2013 by al-Baghdadi, was however rejected by al-Nusra leader al-Julani, and by al-Qaeda leader al-Zawahiri who subsequently cut all ties with ISIL, in February 2014.[4][55][56][57]"
"[DOJ Pride and Serco's 8(a) protégé company Base One Technologies] Information Security Services
Information Security Planning is the process whereby an organization seeks to protect its operations and assets from data theft or computer hackers that seek to obtain unauthorized information or sabotage business operations. Without a properly planned and managed Information Security Plan, an organization runs the risk of law suits, loss of data, compromised operations and loss of reputation. Our experts have secured some of the world largest and most complex commercial and carrier networks, as well as conducted extensive analysis and implementation work on some of the Federal Government's most sensitive and critical environments, such as the FAA [and the Serco-mentored Pentagon Renovation project].
Base One Technologies takes your information security needs seriously! We conduct business analysis, install solutions and protect your network from unauthorized entry and data loss. We are there in the beginning to provide guidance and support to your data security program, through to implementation and eventually during the support life cycle providing process and procedures for incident reporting, analysis and counter measures.
Base One Technologies
Expertly researches, designs, and develops information security policies that protect your data and manage your firm's information technology risk at levels acceptable to your business.
Performs architectural assessments and conducts both internal and external penetration testing. The results of these efforts culminate in an extensive risk analysis and vulnerabilities report.
Develops and implements multi-layer Information Security Solutions, practices and procedures. We deploy Intrusion Detection Systems (IDS) and IP Security with VPN solutions using Cisco routers, Frame Relay, firewalls, address and port translation, obscurity standards and authentication technologies (AAA, 3DES, TACACS, etcŠ), to enhance and meet the level of Data Security required for global organizations.
Conducts IT Security and Risk Assessment in Federal government as well as security testing, implementing security for multiple platforms and operating systems around the world.
Ability to conduct business process analysis to provide technical security countermeasures, risk management and data communications security planning for large organizations.
Provides computer security integration for web server and traditional client-server based applications. We secure environments up to as many layers as required by our clients' policies, industry practices, and regulating bodies - including the desktop and user experience as required. Develops, implements and supports Information Security Counter measures such as honey-pots and evidence logging and incident documentation processes and solutions."
"Originally appeared at Chuck Baldwin LIVE A missionary friend of mine in Eastern Europe recently gave me a heads up regarding an excellent article written by Sebastian Swift entitled "5 Confirmed False Flag Operations And How To Spot Them In The Future."
Swift writes, "The false flag phenomenon is distinctively modern and used as an ideological weapon to control populations with the fear of a manufactured enemy. They are used in ostensibly democratic systems where people believe they have inalienable rights. Such democratic systems--primarily the United States, Israel, and Great Britain--must shock people into sociopolitical and geopolitical consent and, as such, require sophisticated modern propaganda systems and advanced covert operations teams with highly proficient skills."
Here are his telltale signs of a false flag operation:
There is an immediate comprehensive narrative, including a convenient culprit. Law enforcement, government agencies, and the mainstream media immediately proffer a narrative that completely explains the event and encourages citizens to tie their intellectual understanding of the tragedy to the emotions they experience. In his lecture at Contact in the Desert, [author and researcher] Richard Dolan noted that a distinguishing characteristic of a false flag operation is that the official narrative IS NOT questioned by the media. There are often legislative, ideological and sociopolitical power plays waiting in the wings, which the government can immediately implement.
The official narrative has obvious domestic and geopolitical advantages for the governing body. The Bush administration used 9/11 to usher in the War on Terror, which has served as a lynchpin for countless civil liberty infringements by the national security state, including ubiquitous domestic surveillance and indefinite detention.
The narrative behind the attack serves to leverage emotions like fear, as well as patriotism, in order to manufacture consent around a previously controversial issue. For example, many of the recent domestic terror attacks, including the Aurora [and Orlando] shooting[s], have exacerbated and reinforced advocacy of gun control legislation.
Military training drills and police drills occur on the day of and very near the attack itself, causing confusion to obscure eye witness testimony and allowing orchestrators to plant both patsies, disinformation and backup operatives. This is no small point. An incredible percentage of major domestic or international terror attacks have involved simultaneous "training drills.” This list includes, but is not limited to, the infamous NORAD drills of 9/11, the 7/7 London Bombings, the 2011 Norway shooting, the Aurora shooting, Sandy Hook, and the Boston Marathon. Though none of the aforementioned events can be confirmed or denied without a doubt, they bear a striking resemblance to previous false flag attacks and should be looked at with an investigative eye…
Our Founding Fathers believed their government (the British Crown) was deliberately conspiring against them. Thomas Jefferson said as much in our Declaration of Independence:
"Prudence, indeed, will dictate that Governments long established should not be changed for light and transient causes; and accordingly all experience hath shewn, that mankind are more disposed to suffer, while evils are sufferable, than to right themselves by abolishing the forms to which they are accustomed. But when a long train of abuses and usurpations, pursuing invariably the same Object evinces a design to reduce them under absolute Despotism, it is their right, it is their duty, to throw off such Government, and to provide new Guards for their future security."
Read it again: “But when a long train of abuses and usurpations, pursuing invariably the same Object evinces a DESIGN to reduce them under absolute Despotism . . . ." Jefferson and the rest of America's founders believed that there was a “design” (i.e, "plot," "scheme," or “conspiracy,” if you please) to “reduce them under absolute Despotism.” So, if you believe that government conspiracy is only for kooks, you must include America’s Founding Fathers in that group….
Again, I submit if we deliberately "shut our eyes against a painful truth," liberty is not long for this country. And that includes admitting when a tragedy is NOT a conspiracy. But it also means admitting when evidence suggests that it IS."
"UK Cabinet Office – Emergency Planning College – Serco …..Types of Exercise Workshop Exercises
These are structured discussion events where participants can explore issues in a less pressurised environment. They are an ideal way of developing solutions, procedures and plans rather than the focus being on decision making. Table Top Exercises These involve a realistic scenario and will follow a time line, either in real-time or with time jumps to concentrate on the more important areas. The participants would be expected to be familiar with the plans and procedures that are being used although the exercise tempo and complexity can be adjusted to suit the current state of training and readiness. Simulation and media play can be used to support the exercise. Table-top exercises help develop teamwork and allow participants to gain a better understanding of their roles and that of other agencies and organisations. Command/Control Post Exercises These are designed primarily to exercise the senior leadership and support staff in collective planning and decision making within a strategic grouping. Ideally such exercises would be run from the real command and control locations and using their communications and information systems [Feeling lucky, Punk?].
This could include a mix of locations and varying levels of technical simulation support. The Gold Standard system is flexible to allow the tempo and intensity to be adjusted to ensure maximum training benefit, or to fully test and evaluate the most important aspects of a plan. Such exercises also test information flow, communications, equipment, procedures, decision making and coordination. Live Exercises These can range from testing individual components of a system or organisation through to a full-scale rehearsal. They are particularly useful where there are regulatory requirements or with high-risk situations. They are more complex and costly to organise and deliver but can be integrated with Command Post Exercises as part of a wider exercising package."
"Police drop investigation into Serco prisoner transport contract
The outsourcing group said there was no evidence of individual or corporate wrongdoing
By Marion Dakers
7:42AM GMT 19 Dec 2014
The City of London Police has closed an investigation into Serco's prisoner transport contract after more than a year of work, enabling the firm to continue with the contract until 2018.
The Ministry of Justice called in the police in August 2013 to examine whether Serco had misleadingly recorded prisoners as being ready for court when they were not, in order to meet the performance criteria of the contract.
However, Serco said on Friday that the probe into the Prisoner Escort and Custody Services (PECS) contract had been closed after the police found no evidence to support bringing charges against the outsourcing firm or its staff.
"The information obtained was also sufficient for the City of London Police to conclude there was no evidence of any corporate-wide conspiracy or an intention to falsify figures to meet the DRACT [designated ready and available for court time] contract requirement by senior Serco management or at the board level of the company," the firm said in a statement.
The Ministry of Justice had said it would end the contract immediately if the firm’s board was found to have done wrong."
"[DOJ Pride and Serco's 8(a) protégé company Base One Technologies] Information Security Services
Information Security Planning is the process whereby an organization seeks to protect its operations and assets from data theft or computer hackers that seek to obtain unauthorized information or sabotage business operations. Without a properly planned and managed Information Security Plan, an organization runs the risk of law suits, loss of data, compromised operations and loss of reputation. Our experts have secured some of the world largest and most complex commercial and carrier networks, as well as conducted extensive analysis and implementation work on some of the Federal Government's most sensitive and critical environments, such as the FAA.
Base One Technologies takes your information security needs seriously! We conduct business analysis, install solutions and protect your network from unauthorized entry and data loss. We are there in the beginning to provide guidance and support to your data security program, through to implementation and eventually during the support life cycle providing process and procedures for incident reporting, analysis and counter measures.
Key Clients Benefiting From Our Information Security Expertise: Base One Technologies Expertly researches, designs, and develops information security policies that protect your data and manage your firm's information technology risk at levels acceptable to your business.
Performs architectural assessments and conducts both internal and external penetration testing. The results of these efforts culminate in an extensive risk analysis and vulnerabilities report.
Develops and implements multi-layer Information Security Solutions, practices and procedures. We deploy Intrusion Detection Systems (IDS) and IP Security with VPN solutions using Cisco routers, Frame Relay, firewalls, address and port translation, obscurity standards and authentication technologies (AAA, 3DES, TACACS, etcŠ), to enhance and meet the level of Data Security required for global organizations.
Conducts IT Security and Risk Assessment in Federal government as well as security testing, implementing security for multiple platforms and operating systems around the world.
Ability to conduct business process analysis to provide technical security countermeasures, risk management and data communications security planning for large organizations.
Provides computer security integration for web server and traditional client-server based applications.
We secure environments up to as many layers as required by our clients' policies, industry practices, and regulating bodies - including the desktop and user experience as required.
Develops, implements and supports Information Security Counter measures such as honey-pots and evidence logging and incident documentation processes and solutions."
"Government still paying G4S and Serco millions for tagging despite ban
Two firms which faced criminal investigations over alleged overcharging received £13.2m between them after losing contract, analysis shows.
Electronic monitoring tags are used to enforce curfews on more than 100,000 offenders each year.
Photograph: Martin Argles/Guardian
Alan Travis Home affairs editor Thursday 25 June 2015 00.01 BST
Last modified on Thursday 25 June 201511.46 BST
The Ministry of Justice is still paying security firms G4S and Serco millions of pounds every month for supplying electronic tagging equipment, more than a year after both companies were barred from running the contract.
Both companies faced criminal investigations by the Serious Fraud Office over allegations of overcharging that led to them repaying nearly £180m.
The continuing monthly payments to the two companies were uncovered by an analysis of Ministry of Justice (MoJ) data by the Centre for Crime and Justice Studies which shows that G4S was paid a total of £8.7m between March 2014 – when it lost the tagging contract – and February 2015. Serco was paid £4.5m over the same period.
The electronic monitoring tags are used to enforce curfews on more than 100,000 offenders each year. The outsourcing giant Capita took over the contract on an interim basis in April last year. In July 2014, Capita and three other companies were named as the winners of a £265m six-year contract to supply the next generation of satellite tracking tags, which would allow dangerous and repeat offenders to be monitored around the clock.
The MoJ agreed that Capita should continue to use the older G4S/Serco tagging equipment until the first satellite tracking tags were due to come into use by the end of last year.
But there have been continued delays in the development of the satellite tracking tags and the contracts with G4S and Serco to use their equipment have been extended. The Guardian understands that they were given a 15-month extension earlier this year with a further extension possible when that expires in 2016.
Richard Garside of the Centre for Crime and Justice Studies said: "The ministry is continuing to pay G4S and Serco for the supply of electronic tagging equipment months after the contracts should have been terminated, because the timetable for the next generation of satellite tagging technology has slipped and slipped.
"The ministry needs to clarify, as soon as possible, when payments to G4S and Serco will end."
Garside claimed that the MoJ had originally published inaccurate data showing that the two companies had been paid a total of £32m but had since clarified the figure as being £13.2m.
An MoJ spokeswoman said: "G4S and Serco no longer deliver electronic monitoring services. We have always been clear Capita would continue to use their systems until new tags were developed, which gave taxpayers value for money and put public safety first."
She said that the Centre for Crime and Justice Studies' original interpretation of the MoJ data had been incorrect as the bulk of the reported £32m that had been spent had been for the period in 2013 and 2014 when G4S and Serco still held the tagging contract.
The former justice secretary, Chris Grayling, announced in July last year that a small Redditch company, Steatite, would supply the new generation of satellite GPS tracking tags. They in turn sub-contracted to a Taiwanese company, Sanav. But it is understood that the first Steatite tags were rushed into use last year in an attempt to meet Grayling's end-of-year deadline, but had to be withdrawn amid a dispute over intellectual property rights and other issues. The tags may not be ready until 2016 or later.
G4S runs the largest current satellite tracking programme in the world in France where it tracks the daily movements of 12,000 offenders. A G4S spokesman said: "Our GPS-enabled electronic monitoring technology is a world-leader – designed, developed and exported from our base in Leicester to 17 countries around the world – and we will continue to support the ministry of justice in England and Wales in any way we can."
This article was amended on 25 June 2015 to make it clear that Steatite, not Capita, was responsible for the delays in the development of the satellite tags."
"[White's Club member] Rupert Christopher Soames OBE (born 18 May 1959) is a British businessman, CEO of the outsourcing company Serco.[1] Soames was born in Croydon, Surrey, to Lord and Lady Soames. He is a grandson of Sir Winston Churchill, a nephew of the former Defence Secretary Duncan Sandys and Diana Churchill; the journalist Randolph Churchill and the actress and dancer Sarah Churchill and a great-nephew of the founders of the Scout movement, Robert Baden-Powell and Olave Baden-Powell. His brother is the Conservative MP Sir Nicholas Soames.
Education[edit]
Soames was educated at St. Aubyns Preparatory School in Rottingdean, East Sussex and Eton College,[2] and then Worcester College at the University of Oxford,[3] during which time he worked as a DJ at the London nightclub Annabel's, as well as being elected to the Presidency of the Oxford Union.[3]
Career[edit]
Upon graduation, he was offered a position at General Electric Company (GEC) by the managing director Arnold Weinstock. He remained at GEC for 15 years, working in the company's avionics and computing divisions, and became managing director of Avery Berkel, running the company's UK, India, Asia and Africa operations.[4]
After leaving GEC in 1997, Soames joined the software company Misys as chief executive of its Midas-Kapiti division. He was promoted to chief executive of the Banking and Securities Division in June 2000.[5]
Soames left Misys after a disagreement with Misys founder Kevin Lomax on the company's direction, and was appointed chief executive of power hire group Aggreko in June 2003,[6] replacing Philip Harrower who died when his car collided with a train in the United States.[7]
Soames was appointed Officer of the Order of the British Empire (OBE) in the 2010 New Year Honours.[8] In November 2010 Rupert Soames gave a speech to Holyrood in which he warned, "In the UK, we are already close to the rocks, because, over the next 8 years a third of our coal-fired capacity, two-thirds of our oil-fired capacity, and nearly three-quarters of our nuclear capacity will be closed down either through age or the impact of the European Large Combustion Plant Directive. Absent a massive and immediate programme of building new power stations, with concrete being poured in the next two years, we will be in serious danger of the lights going out."
"Serco do a bunch more that didn't even make our story: As well as thanking God for his success, CEO Chris Hyman is a Pentecostal Christian who has released a gospel album in America and fasts every Tuesday. Amazingly, he was also in the World Trade Centre on 9/11, on the 47th floor addressing [Serco] shareholders Serco run navy patrol boats for the ADF, as well as search and salvage operations through their partnership with P&O which form Defence Maritime Services. Serco run two Australian jails already, Acacia in WA and Borallon in Queensland. They're one of the biggest companies In the UK for running electronic tagging of offenders under house arrest or parole."
"Serco farewell to NPL after 19 years of innovation
8 January 2015
Sercosaid goodbye to the National Physical Laboratory (NPL) at the end of December 2014 after 19 years of extraordinary innovation and science that has seen the establishment build a world-leading reputation and deliver billions of pounds of benefit for the UK economy. During that period under Serco's management and leadership, NPL has delivered an extraordinary variety and breadth of accomplishments for the UK's economy and industry. Some of the key achievements during that time have been:… It has been estimated that work carried out by the Centre of Carbon Measurement at NPL will save eight million tonnes of carbon emissions reductions (2% of UK footprint) and over half a billion pounds in economic benefit over the next decade….
NPL's caesium fountain atomic clock is accurate to 1 second in 158 million years and NPL is playing a key role in introducing rigour to high frequency trading in the City through NPL [Zulu] Time."
Field McConnell, United States Naval Academy, 1971; Forensic Economist; 30 year airline and 22 year military pilot; 23,000 hours of safety; Tel: 715 307 8222
David Hawkins Tel: 604 542-0891 Forensic Economist; former leader of oil-well blow-out teams; now sponsors Grand Juries in CSI Crime and Safety Investigation







No comments:
Post a Comment
Note: Only a member of this blog may post a comment.